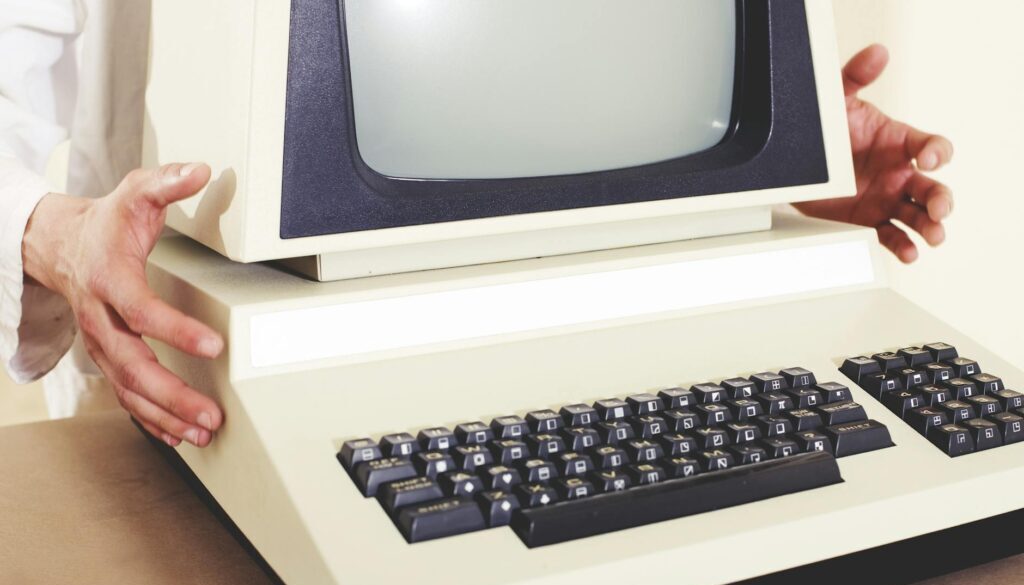
Secure Your Hardware: The Foundation of Cyber Resilience
Hardware is often overlooked in cybersecurity, but it’s the bedrock of your defences. Weak or unprotected devices open the door to attackers, while strong hardware controls give you fewer entry points, better endpoint control, and a safer base for everything else.
Top Tips for Securing Hardware:
Choose Trusted Devices
Buy hardware from reputable vendors with verified firmware.
Ensure devices support modern security features (e.g., TPM, Secure Boot).
Lock Down BIOS/UEFI Settings
Disable Unused Ports & Interfaces
Switch off unused USB, FireWire, or SD ports in BIOS/UEFI.
Restrict or monitor USB device use to avoid rogue storage or malware.
Physically Secure Systems
Use cable locks for laptops and secure racks for servers.
Restrict access to network hardware (routers, firewalls, switches).
Enforce Device Policies
Control Peripheral Use
Harden Endpoint Configurations
Apply OS hardening guides (CIS Benchmarks, vendor security baselines).
Remove unnecessary pre-installed apps (“bloatware”) that add risk.
Monitor & Audit Hardware Regularly
Remember: A single unprotected device, or one rogue USB stick, can undo your entire cybersecurity strategy. Secure the foundation, and every layer above it becomes stronger.